During the years, cybersecurity certifications have been considered to be the golden standard of demonstrating security competence. They are used to find professionals, evaluate the capacity of vendors, and develop confidence in their security stance by organizations. Although certifications are indeed very useful in creating basic knowledge, the increasing cases of real-life breaches indicate a monumental fact that certifications in themselves do not ensure security.
Hacking attacks are not examination based. It is the amount of credentials a team has that does not matter to an attacker, instead, they seek dismissed logic errors, misconceptions, and poor assumptions. This is where skill based security authentication is not only useful, but mandatory.
What Certifications Are Good At
The idea of certification is to confirm the knowledge of concepts, tools, frameworks, and best practices. They make certain that the professionals are knowledgeable of the security principles, industry standards and frequently encountered vulnerability classifications. This systematic learning is very practical to novices and developing teams.
Nonetheless, the majority of certifications are used in regulated settings. The situations are foreseeable, the area is clear and answers can be known beforehand in many cases. This establishes a disconnection between theory and practice.
The Real-World Security Gap
Vulnerabilities in the real world are not usually found isolated. Even a small misconfiguration and inadequate access control together with faulty business logic can result in a critical compromise. These are chained problems that cannot be identified with the help of checklist-based tests or automated scans–and hardly tested in certification exams.
There are numerous security incidents with high impact, yet teams fail to detect them due to the fact that the systems have never undergone such testing as the attackers do. Being aware of what a vulnerability is does not necessarily imply the knowledge of how to locate, exploit it in a manner that is responsible and an evaluation of its actual business consequences.
What Skill-Based Security Validation Looks Like
Skill-based validation emphasizes on the ability not the credentials. It answers questions such as:
- Can a tester identify non-obvious attack paths?
- Can they adapt when initial exploitation attempts fail?
- Can they explain risk in a way that developers and decision-makers understand?
This strategy resembles the way that real attackers do the same experimentation, adaptation, and creative thinking. It puts greater emphasis on practical testing to live environments where the assumptions are violated and some unpleasant surprises appear.
Why Live Hacking and Bug Bounty Models Matter
Live hacking environments and bug bounty programs offer ongoing and real-world testing to a variety of security researchers. Rather than one assessment or annual audit, organizations are able to access various points of view and dynamic attack methods.
Social sites such as Bugv allow organizations to test security on a real basis instead of basing it on perceived preparedness. The vulnerabilities are identified, confirmed and prioritized according to actual exploitability- and not hypothetical risk.
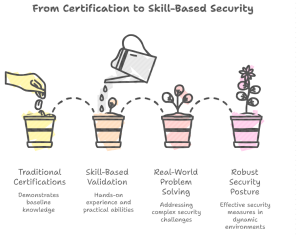
Turning Validation into Action
Credentialing is no longer sufficient in modern security, and demands evidence. Skill-based validation assists organizations to shift the assumption to assurance, a compliance-based check to actual reduction of risk.
In order to find out how your systems can be resistant to real-world attackers, Bugv helps you to test them in practice, not only on paper.
Bugv provides organizations with verified security researchers through live hacking programs and skill-based validation in order to find what automated tools and certifications frequently fail to identify.