Compliance is the starting and stopping point of cybersecurity activities to many organizations. Satisfaction of regulatory obligations, auditing and verification of security boxes tend to give an illusion of security. But high profile breaches keep on being a bitter pill to swallow: compliance does not equal security.
The compliance frameworks are meant to provide minimum controls but not to protect against actual attackers. Although they are a crucial element in governance and risk management, compliance alone creates critical weaknesses that are fast to be exploited by the attackers.
What Compliance Actually Delivers
The compliance standards are centered on the policies, documentation and predetermined controls. They assist organizations in proving that security processes are present and that there is some minimum protection. This will be vital in accountability, regulatory trust and operations consistency.
Nonetheless, compliance checks tend to be time constrained and foregone. They test the presence not the effectiveness of controls in the face of attack. Therefore, companies can survive audits, but they can still be exposed to practical attacks.
The Illusion of Security
An obedient system may still harbor very serious vulnerabilities. Chained exploits, business logic flaws, and insecure assumptions can be out of the range of the traditional audits. Checklists are not adhered to by attackers, but opportunity.
Most of the breaches happen in an environment that was technically compliant upon the occurrence of the breach. It is not the policy lack, but the practical validation lack. On paper, security can break down when it is put to the test.
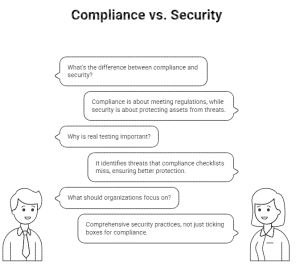
Why Real Testing Changes the Equation
It is a simulation of the actions of attackers by real testing. It consists of system probing, chaining vulnerabilities, testing assumed weaknesses and threats that are frequently overlooked by automated tools and audits.
Hands-on testing answers critical questions:
- Can access controls actually be bypassed?
- Do monitoring systems detect abuse in real time?
- How does the system respond when things go wrong?
Continuous Validation in a Changing Environment
Current applications are changing fast. New attack surfaces are added as new features, integrations and deployments are introduced continuously. A once-year compliance check is not able to cope with this change.
Actual testing of controls, particularly when done periodically, gives a continuity of guarantee regarding the effectiveness of security controls in the face of emerging technology. It changes the periodical security obligation into an active defense policy.
Moving Beyond Checkboxes
The aspect of compliance must not be considered an endpoint. The idea of true security presupposes the verification of controls against real-life conditions and adjustment to the real outcomes.
Services such as Bugv can assist organizations to go beyond checkbox security, providing live and skill-based testing by skilled security researchers. This is a way of making known the behavior of systems under actual attack, rather than their image according to reports.
Call to Action
When your organization is only using compliance to address security, you might be looking at half of the risk. Bugv provides real-world security testing as a form of live hacking and practical testing, which assists in detecting what is usually overlooked in the process of auditing.
Since the real security is not established in the documents, it is established in practice.