The term “zero-day” refers to a software flaw that is discovered and potentially exploited before the software vendor has had even a single day to address it. There is no patch, no workaround, and often no warning. These vulnerabilities are particularly dangerous because defenders are essentially blind to the threat until damage has already been done.
Why Zero-Days Are So Dangerous
Unlike known vulnerabilities that organizations can patch proactively, zero-days leave no window for preparation. Attackers whether nation-state actors, cybercriminal groups, or independent hackers may exploit a zero-day silently for months before detection. During this window, they can exfiltrate data, install persistent malware, disrupt critical infrastructure, or escalate privileges deep within a network.
The commodification of zero-days has created an underground economy where these exploits are bought and sold for enormous sums. A critical zero-day in a major operating system or browser can command prices ranging from $500,000 to over $2.5 million on the grey and black markets.

How They Are Discovered
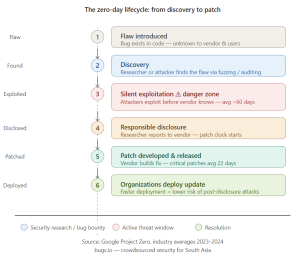
Zero-day vulnerabilities are discovered through several pathways. Security researchers use fuzzing (feeding random or malformed input to software), static code analysis, and reverse engineering of compiled binaries to uncover logic flaws. Increasingly, bug bounty programs like those hosted on platforms such as Bugv have become a primary mechanism for responsible discovery. Researchers are incentivized financially to find and disclose vulnerabilities before bad actors do.
The Role of Bug Bounty Programs in Zero-Day Defense
Governments and corporations alike have recognized that traditional security testing cannot keep pace with the complexity of modern software. Bug bounty programs crowdsource vulnerability discovery to thousands of independent researchers around the world. This approach is statistically more effective than internal security teams working alone.
Platforms like Bugv bridge the gap between organizations and ethical hackers across South Asia, enabling companies to proactively discover vulnerabilities before they become zero-days. By offering structured reward programs, Bugv incentivizes responsible disclosure rather than exploitation, keeping the regional digital ecosystem significantly safer.
What Organizations Must Do
No organization can completely eliminate zero-day risk, but exposure can be substantially minimized. Maintaining a rapid patch deployment process, enabling vulnerability disclosure channels, subscribing to threat intelligence feeds, and engaging in continuous penetration testing are all essential defensive layers. Most importantly, treating security as an ongoing process not a one-time audit is the foundation of true cyber resilience.
Let Ethical Hackers Find Your Zero-Days First
The most dangerous aspect of a zero-day is not the vulnerability itself it is the silence before discovery. Bugv’s bug bounty platform puts a community of skilled ethical hackers to work on your systems continuously, dramatically shrinking the window between a flaw existing and it being responsibly reported. Rather than waiting for a breach to reveal your weaknesses, partner with Bugv and turn the unknown into the known before an attacker does it for you.