Startups are fast moving- and you can see why not. However, as usual, speed is the distinction between growth and irrelevance. However, when competing on features, security is often considered a problem to solve later on. Regrettably, attackers do not wait until the startups grow.
Startups do not have many security incidents that are advanced attacks. They are caused by simple and preventable weaknesses that fall through in the fast development.
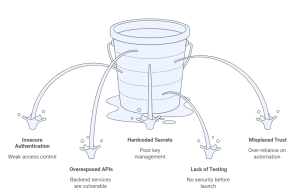
Insecure Authentication and Access Control
Broken access control is one of the most widespread problems in the early-stage products. Features are constructed in a short time, roles are soft and assumptions are made on the user behaviour.
This often leads to:
- Users accessing data they shouldn’t
- APIs trusting client-side input too much
- Admin functionality exposed without proper checks
They are not frequent in automated scans, yet attackers can easily exploit these issues when they run tests of authorization logic by hand.
Overexposed APIs and Backend Services
APIs are very critical to startups: web apps, mobile apps, and third-party integrations. In most instances, APIs are released in a loose manner, low rate limiting, or inadequate authentication.
Attackers routinely look for:
- Endpoints that were meant for internal use
- Missing object-level authorization
- APIs that expose excessive data
Once discovered, these weaknesses can lead to data leaks or full account compromise.
Hardcoded Secrets and Poor Key Management
The challenges with speed-driven development are that secrets are frequently hardcoded into the source code, mobile application, or configuration files. API keys, tokens, and credentials are also occasionally reused between environments or not rotated at all.
In case these secrets are compromised, even accidentally, they will allow direct access to crucial systems.
Lack of Security Testing Before Launch
Most startups only perform functional test to prove features. Even when security testing occurs, it comes too late.
This brings about a high-risk point where vulnerabilities are straight into the production. Unless there is a adversarial test, the teams might never know how their application performs when it is being abused.
Misplaced Trust in Automation
Automated scanners and security tools are handy, but do not comprehend business logic, how users work, or the intent. At an early stage, teams tend to believe that they are safe enough as they pass through the automated check exercises.
As a matter of fact, logic-based high-impact vulnerabilities in startups are numerous and need human creativity to identify.
How Startups Can Reduce Risk Early
Innovation does not need to be slowed down by security. Uncomplicated measures, like ensuring access controls, examining API exposure, and testing real attack paths, are effective risk mitigation measures without impeding development.
Startups can attract the attention of external security researchers as early as possible and thereby uncover the important problems before the attacker does. It also assists the teams to learn the point of their assumptions failure.
Services such as Bugv allow startups to test the effectiveness of their security with live application hacking, and not automated systems or periodic testing. This method offers practical experience, as well as promotes the fast development.
Call to Action
When you are developing quick, you ought to be smarter in testing. Bugv assists early startups in discovering actual vulnerabilities by testing via live and skill-based security tests, making security a growth facilitator, rather than an inhibitor.
Since it is always easy to fix vulnerabilities earlier than it is to explain vulnerabilities later.