Locating an actual vulnerability and subsequently forfeiting the bounty due to a report that was not written correctly is one of the most frustrating outcomes when it comes to bug bounty hunting. It occurs frequently than it ought to. These are the errors that beginners lose payouts, credibility and time.
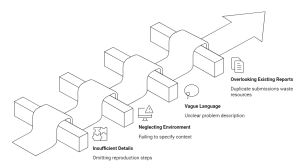
1. Vague Titles That Say Nothing
The title is the first thing that a triage team reads. Such a title as XSS vulnerability found reveals little to them. Where was it found? What is the impact? It would be more suitable to have in its title the following: Stored XSS on profile bio field with session hijacking of other users. Specific titles are taken seriously. Anonymous ones are demoted.
2. Missing or Incomplete Reproduction Steps
It is the most frequent cause of invalid bugs being billed as so. The triage team is unable to confirm your finding should they fail to reproduce it by the steps you have followed. Brief your reproduction instructions so that the reader does not have to scroll up and down the application a multitude of times to discover what to do. Add all the clicks, all the inputs, all requests. Assume nothing is obvious.
3. Overstating Severity
Novices tend to evaluate all things as severe with the prospects of getting a better reward. Triage teams pick up on this right away and this hurts your credibility on all reports that you file going forward. A reflected XSS that has a minor impact is not critical. Honesty in rating with the program guidelines or CVSS scoring. Correct severity rating builds credibility among the triage teams with time.
4. No Proof of Concept
It is not sufficient to describe a vulnerability but not prove it. Add screenshots, screen recordings, or get requests and responses of Burp Suite. In case of injection vulnerabilities, present the payload and the output. To access control, present the request which accessed unauthorized information and the response which verified it. Facts make a statement into a proven truth.
5. Out of Scope Issues Reporting.
Each bug bounty program has a scope, or a list of assets and types of vulnerabilities that can be rewarded. Reporting on areas, sub areas, or types of vulnerability that are explicitly out of scope wastes your time, and time of the triage team. You must read the program rules carefully when you are about to begin testing, and again when you are submitting anything.
6. Theoretical Vulnerabilities Submission.
A vulnerability that will only be exploited by an improbable sequence of situations, or one that you have not proven actually. Bug bounty programs are based on demonstrated and proven impact. In case you are unable to prove that the vulnerability is real and can be exploited in its current form in the application, continue testing until it can.
7. Weak Communication Once Submitted.
Beginners who place a report and remain silent, or worse, send follow-up messages a couple of times in hours saying that there should be an update. Triage takes time. In case of a request to provide more information then respond well and timely. In case you do not agree with a severity rating, then argue out your case in a professional manner. Your wording upon submission helps to influence the reception of your future reports.
The Underlying Problem
These errors are mostly as a result of haste. A researcher just stumbles on something that appears interesting and becomes excited and then submits without the report being prepared. To take the report as seriously as the research itself is what makes the difference between hunters who get paid and those who do not.
Writing a good bug report is just as important as finding the vulnerability itself. Clear explanations, reproducible steps, and honest severity ratings make the difference between a rejected report and a rewarded one. As you continue improving your reporting skills, practicing on real bug bounty programs can accelerate your growth. Platforms like Bugv give security researchers the opportunity to test their skills, submit responsible reports, and earn rewards for real vulnerabilities. If you want to start submitting professional-quality bug reports and turn your findings into real impact, explore active programs today at Bugv.