Firewalls, encryption, multi-factor authentication organizations invest heavily in technical defenses. But when an attacker can simply ask an employee for their credentials, impersonate an executive, or manufacture a sense of urgency that bypasses rational thinking, no amount of technology is sufficient. This is the essence of social engineering: manipulating people rather than machines.
Attackers now leverage AI-generated voice cloning, deepfake video calls, and hyper-personalized phishing powered by data scraped from social media. The attacks are more convincing, more targeted, and more damaging than ever before.
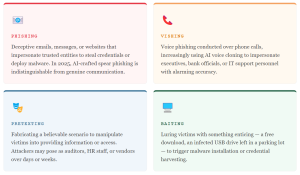
The Four Core Attack Vectors
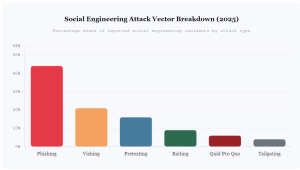
Social engineering attacks take many forms, but most fall into four primary categories, each exploiting a different aspect of human behavior and trust.
Why It Works: The Psychology Behind the Attack
Social engineers do not exploit software, they exploit cognitive biases. The most commonly weaponized psychological triggers include:
Authority: People instinctively comply with requests from those in perceived positions of power. An email appearing to come from the CEO demanding urgent wire transfer approval is a classic example.
Urgency: Creating artificial time pressure disables careful deliberation. “Your account will be suspended in 24 hours” bypasses rational evaluation.
Social proof: Humans are more likely to act when they believe others are doing the same. Fake testimonials and fabricated colleague endorsements exploit this effectively.
Fear: Threat of punishment, legal action, or financial loss drives victims to act without verification.
How to Defend Against the Human Threat
Technical controls alone cannot stop social engineering. A comprehensive defense strategy must treat people as a security layer, one that requires continuous investment, just like any technical system.
Organizations must implement regular security awareness training that goes beyond annual compliance checkboxes. Simulated phishing exercises, real-time coaching, and clear reporting mechanisms dramatically reduce susceptibility. Equally important is establishing verification protocols no financial transaction, credential reset, or access grant should be authorized based on a single communication channel alone, regardless of how convincing the request appears.
Red Flags Every Employee Should Recognize
- Unexpected requests for credentials, payments, or sensitive data via email or phone
- Artificial urgency “You must act now or face consequences”
- Requests to bypass normal procedures “just this once”
- Unsolicited attachments or links, even from known contacts
- Callers who know personal details but cannot verify their identity through official channels
- Too-good-to-be-true offers, prizes, or exclusive access
The Role of Security Testing
One of the most effective ways to measure and improve human resilience is through controlled social engineering assessments, ethical simulations that test how employees respond to real-world attack scenarios. These assessments, conducted through structured bug bounty programs and penetration testing engagements, reveal gaps in awareness training and organizational culture that no automated scanner can detect.
Your Strongest Defense Starts with Your People
Bugv’s platform connects organizations with ethical security researchers who test not just your systems, but your human attack surface helping you identify and close the gaps that social engineers exploit. Because the best firewall is an informed workforce.