Almost every digital product built today relies heavily on Application Programming Interfaces (APIs). From the login button on a mobile app to the payment gateway on an e-commerce platform, APIs are the connective tissue of the digital economy. But this ubiquity comes at a significant cost: APIs are frequently deployed without the same security rigor applied to traditional application layers, making them a prime target for attackers.
Unlike conventional web application attacks that are relatively well-understood, API attack s are often invisible to traditional security tools. Firewalls and web application firewalls that perform well against standard HTTP traffic frequently miss API-layer attacks because the traffic appears legitimate on the surface. By the time a breach is detected, the damage data exfiltration, account takeover, service disruption is often already complete.
The Most Critical API Vulnerabilities
The Open Web Application Security Project (OWASP) maintains a dedicated API Security Top 10 list a reflection of how serious and distinct the API threat landscape has become. At the top of this list sits Broken Object Level Authorization (BOLA), where attackers manipulate object IDs in API requests to access data belonging to other users. It is extraordinarily common and often trivial to exploit, yet it continues to be overlooked during development.
Closely related is Broken Authentication poorly implemented token validation, missing session expiry, or weak API key management that allows attackers to impersonate legitimate users. Broken Function Level Authorization is equally dangerous: administrative API endpoints accessible to regular users due to absent role checks, enabling privilege escalation and unauthorized system actions. Rounding out the top concerns are Security Misconfiguration default settings, open CORS policies, verbose error messages and Unrestricted Resource Consumption, where missing rate limits allow attackers to conduct denial-of-service attacks or mass data scraping at virtually no cost.
Why API Security Is Systematically Neglected
The root cause of most API security failures is not purely technical, it is organizational. Development teams ship APIs rapidly under deadline pressure. Security reviews are treated as an afterthought, if they occur at all. APIs multiply quickly across microservices architectures, creating shadow APIs active endpoints in production that are unknown to the security team. Research estimates that the average large organization has hundreds of such undocumented endpoints, each receiving no monitoring, no authentication review, and no rate limiting.
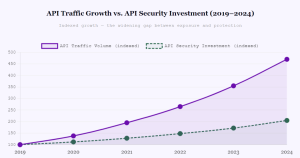
Compounding this is the widening gap between API adoption and API security investment. Traffic volumes have grown nearly fivefold since 2019, yet security tooling and budget allocation have barely doubled over the same period. Organizations are deploying more APIs faster than they can secure them and attackers have taken full notice.
How to Secure Your APIs Effectively
Effective API security begins with visibility. Organizations must maintain a complete, continuously updated inventory of every API endpoint including internal, partner, and third-party APIs. Without this foundation, no security measure can be consistently applied. From there, every endpoint must enforce authentication and strict authorization checks server-side. It is not sufficient to trust that the client will only call permitted endpoints; the server must verify every request independently.
Rate limiting, payload size restrictions, and API gateway enforcement are non-negotiable for any production system. But perhaps the most powerful investment an organization can make is in continuous, human-driven API testing. Automated scanners are effective at identifying known vulnerability patterns, but they routinely miss complex authorization flaws, logic errors, and chained attacks that skilled ethical hackers catch reliably. Bug bounty programs that include API scope specifically provide a cost-effective mechanism for ongoing discovery turning the creativity of the security research community into a permanent defensive asset.
Your APIs Are Open. Are You Sure to Whom?
Bugv’s ethical hacking community specializes in API security assessments finding the broken authorizations, shadow endpoints, and misconfigurations that automated scanners miss. Launch a targeted API bug bounty program with Bugv before an attacker finds what your tools overlooked.