The general belief within the security community is that SQL Injection is an obsolete issue that was fixed back in the early 2000s and that developers no longer need to be concerned about the issue in the current era. This assumption is wrong. SQL Injection is among the most common vulnerabilities identified in bug bounty programs in 2026, and at that, it is nearly always of critical or high severity.
What Is SQL Injection?
SQL Injection takes place when the input provided by the user is injected into a database query without its appropriate sanitization. This enables the attacker to control the logic of the query – obtaining data, getting around authentication, altering records or even running commands on the server it is operating on in certain instances.
A vulnerable login query looks like this:
SELECT * FROM users WHERE username = '[input]' AND password = '[input]'
An attacker can inject ‘ OR ‘1’=’1 to bypass authentication entirely. This is one of the simplest forms, and it still works against a surprising number of real applications today.
Why Is It Still Being Found in 2026?
- Legacy codebases are the biggest reason. Applications that are being operated by many organizations were developed years or decades ago when secure coding was not a standard practice. Raw query construction is sprinkled across these systems, and hardly audited.
- Rapid development is another factor. Small teams and startups that are working under pressure to deliver tend to omit security reviews. The problem of input validation becomes secondary.
- Inconsistent use of ORMs also plays a role. Even when all other code is secure, developers integrating raw queries into applications that use ORM create vulnerabilities in particular endpoints of these applications.
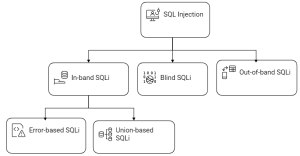
Types of SQL Injection You Should Know
- In-band SQLi is the most straightforward ,where the results are displayed as the response of the application. This consists of error based and union based injection.
- Blind SQLi, the application does not actually give out query results, but instead it carries out differently depending on the truth of a condition or not. It is more patient and is equally exploitable.
- Out-of-band SQLi transfers data via a different channel like in DNS or HTTP requests by the database itself. Not prevalent, but potentially very strong in limited settings.
Where to Look During Testing
Attention on any location where the user input is processed and a database interaction is probable:
- Login forms and authentication endpoints
- Search bars and filter functions
- URL parameters and query strings
- API endpoints that accept structured data
- Hidden form fields and cookies passed to backend queries
Automated tools such as SQLMap can help with the detection, though it is more helpful to be able to test manually. Automated tools will overlook context-based injections that a human tester will identify.
Why It Is Still Critical
An established SQL Injection flaw will provide an attacker with direct access to your database. This may imply:
- Full exposure of user data including passwords, emails, and personal information
- Authentication bypass without valid credentials
- Ability to modify or delete records
- In some configurations, remote code execution on the server
This is one of the reasons why SQL Injection always receives critical or high criticality in bug bounty programs. There is hardly conceptual potential influence.
The Bottom Line
SQL Injection is not a novice subject, which one learns and forgets. It is a practical and practical vulnerability category, which is manifested in production systems on a daily basis, even in the companies that consider themselves secure. Whether you are under bug bounty programs or not, it must always be on your list of testing even though the application may seem very modern.
The applications which are hit are not necessarily old or poorly built. They tend to be the case when one developer, on one end, was not practicing the same as the other team members.
SQL Injection remains a persistent threat in 2026, lurking in even the most modern applications due to legacy code, rushed development, and inconsistent practices. Don’t let outdated assumptions leave your systems exposed prioritize thorough testing, adopt prepared statements and ORMs rigorously, and stay vigilant in every code review. Ready to fortify your defenses? Partner with Bugv.io for expert vulnerability assessments and bug bounty programs that catch these critical flaws before attackers do: https://bugv.io/.